Worm.Banker.af
Cuadro de Mando de Amenazas
Cuadro de mando de amenazas EnigmaSoft
EnigmaSoft Threat Scorecards son informes de evaluación de diferentes amenazas de malware que nuestro equipo de investigación ha recopilado y analizado. Los cuadros de mando de amenazas de EnigmaSoft evalúan y clasifican las amenazas utilizando varias métricas que incluyen factores de riesgo reales y potenciales, tendencias, frecuencia, prevalencia y persistencia. Los cuadros de mando de amenazas de EnigmaSoft se actualizan regularmente en función de nuestros datos y métricas de investigación y son útiles para una amplia gama de usuarios de computadoras, desde usuarios finales que buscan soluciones para eliminar malware de sus sistemas hasta expertos en seguridad que analizan amenazas.
EnigmaSoft Threat Scorecards muestra una variedad de información útil, que incluye:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Nivel de severidad: El nivel de severidad determinado de un objeto, representado numéricamente, basado en nuestro proceso de modelado de riesgo e investigación, como se explica en nuestros Criterios de evaluación de amenazas .
Computadoras infectadas: la cantidad de casos confirmados y sospechosos de una amenaza particular detectada en computadoras infectadas según lo informado por SpyHunter.
Consulte también Criterios de evaluación de amenazas .
| Popularity Rank: | 19,765 |
| Nivel de amenaza: | 80 % (Elevado) |
| Computadoras infectadas: | 6,147 |
| Visto por primera vez: | July 24, 2009 |
| Ultima vez visto: | January 31, 2026 |
| SO(s) afectados: | Windows |
El Worm.Banker.af es una seria infección informática de gusano que tiene la capacidad de modificar o tomar el control de las funciones de la computadora. Es capaz de abrir una puerta trasera para que un atacante remoto se infiltre en el sistema. Permitiendo a los criminales cibernéticos acceder a los datos personales almacenados en el disco duro. Se conoce también como Worm/Banker.B.1, Banker.worm.af, PWS-Banker o Banker.af.Banker.worm ....
Tabla de contenido
Alias
4 proveedores de seguridad marcaron este archivo como malicioso.
| Antivirus Vendor | Detección |
|---|---|
| Sophos | Mal/Emogen-K |
| Panda | Trj/Banker.LIN |
| F-Secure | IM-Worm.Win32.Banker.af |
| AntiVir | HEUR/Malware |
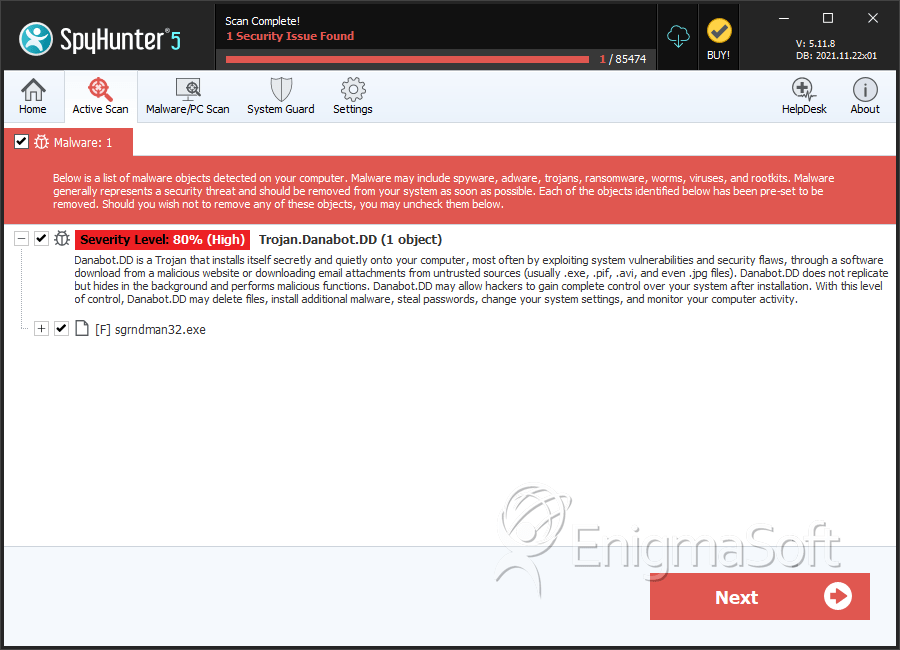
SpyHunter detecta y elimina Worm.Banker.af
Detalles del Sistema de Archivos
| # | Nombre | MD5 |
Detecciones
Detecciones: la cantidad de casos confirmados y sospechosos de una amenaza particular detectada en computadoras infectadas según lo informado por SpyHunter.
|
|---|---|---|---|
| 1. | sgrndman32.exe | 83c3303fe6bb34655c7e0c1395ee58d6 | 0 |
Reporte de análisis
Información general
| Family Name: | Trojan.Danabot.DD |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
9eb58bda85f7fb02f2cf7a2ee45a1dc6
SHA1:
13c633add14c99b6ca3ccddf84fe8d8222623a30
SHA256:
A40AC79E163E4A169209573E0FCDD3E4851AC68DB662B8DB2D523DFF7C716D4F
Tamaño del archivo:
1.48 MB, 1476624 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- 2+ executable sections
- dll
- ntdll
- VirtualQueryEx
- WriteProcessMemory
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 3,257 |
|---|---|
| Potentially Malicious Blocks: | 24 |
| Whitelisted Blocks: | 2,859 |
| Unknown Blocks: | 374 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Danabot.L
- Delf.NL
- Guildma.D
- Injector.FZ
- InstallMonstr.EA
Show More
- Ponteiro.E
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \device\namedpipe\gmdasllogger | Generic Write,Read Attributes |
| c:\programdata\b384ff90 | Synchronize,Write Attributes |
| c:\programdata\b384ff90\991a8995 | Synchronize,Write Attributes |
| c:\programdata\b384ff90\9e8c8d6d | Synchronize,Write Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
| Encryption Used |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\13c633add14c99b6ca3ccddf84fe8d8222623a30_0001476624.,LiQMAxHB
|
